- Comparison
- FocalFlow vs Loom
- FocalFlow vs Screen Studio
- About
- Discover EaseUS
- Reviews & Awards
- License Agreement
- Privacy Policy
- Student Discount

With remote work becoming the new norm for corporate operations, the demand for screen recording technology is experiencing explosive growth. According to a Gartner report, "In the post-pandemic future, approximately 48% of employees will continue to work remotely to some extent, a significant increase from the pre-pandemic figure of 30%." (Source: Gartner)
Meanwhile, other surveys also indicate that about 28% of employees worldwide are currently working remotely, and in the United States, it is projected that 22 million people (a substantial proportion of the workforce) will be working remotely by 2025. (Source: DemandSage, 2025). Such a large population of remote workers has deepened the reliance on screen recording tools in scenarios such as online education, SaaS product demonstrations, gaming live streaming, and remote medical collaboration.
However, while screen recording enhances efficiency and transparency in collaboration, it also brings significant security and privacy risks. Unauthorized recording, data leakage, lack of storage encryption, non-compliance with regulations, and even hackers exploiting malware to monitor users' screens are frequent occurrences, making user information highly susceptible to exposure or misuse.
Therefore, this report by EaseUS aims to conduct an in-depth analysis of the various security risks and privacy challenges associated with screen recording scenarios. It also proposes systematic countermeasures based on multi-layered (user, technological, compliance, and device) protection strategies to help users and enterprises build a trustworthy and secure recording ecosystem that complies with regulations.
Understanding these risks is crucial for anyone who uses screen recording tools, whether for personal or professional reasons. Let's delve into the major risks associated with screen recording and how they can impact users' security and privacy.
Screen recording files are essentially high-sensitivity data, often containing corporate strategic documents, financial statements, customer information, login credentials, and intellectual property content. Their lifecycle can be summarized as: Collection → Storage → Sharing. There are potential risks at each stage:
Sensitive Content Leakage
Screen recordings may inadvertently capture sensitive information such as account passwords, credential information, financial records, customer data, and source code. If these recording files are not encrypted, mistakenly uploaded, or disseminated, the consequences could be disastrous.
Unauthorized Access and Misuse
If screen recording files are not properly secured with access permissions, internal personnel or hackers may easily gain unauthorized access. If access rights to the recording files are obtained through software vulnerabilities or lax permission configurations, these individuals can easily steal and misuse the content.
Transmission and Storage Risks
Unencrypted recording files are susceptible to man-in-the-middle (MITM) attacks, interception, or tampering during transmission. Similarly, if stored in the cloud or shared drives without encryption, they are also vulnerable to attacks.
For example, the Verizon 2025 Data Breach Investigations Report indicates that over 22% of data breaches involve credential abuse, and screen recording is one of the high-risk channels for such leaks. (Source: Verizon)
Here we use a table to show you the general process of the screen recording file life cycle and possible risk factors:
| Phase | Core Description | Key Security Weaknesses |
|---|---|---|
| Collection | Generation phase of screen recordings, including screen and audio recordings. |
|
| Storage | Screen recordings are saved to local or cloud storage. |
|
| Sharing | Screen recordings shared via email, cloud services, instant messaging, etc. |
|
Unauthorized Recording
In scenarios such as multi-person video conferences and online teaching, if participants are not informed in advance that the session is being recorded, it may infringe on users' right to privacy and informed consent, reducing trust in the platform. This violates the "explicit consent" principle in GDPR and PIPL.
Abuse of Malicious Monitoring Tools
Hackers may use Trojan programs or other malicious software to secretly activate screen recording functions, allowing them to monitor users' activities over the long term, record their actions, and even capture communication details, severely infringing on privacy rights.
Screen recording directly involves the processing of personal information and the compliance of content usage. Different regions have distinct legal requirements for personal information and recorded content:
Additionally, the recording process may involve other people's copyrights or trade secrets. Without authorization, there is a high risk of infringement.
Under the strict enforcement of GDPR, non-compliant companies face severe fines. For example, Meta was fined €1.2 billion for illegally transferring EU user data to the United States, setting a record for the highest penalty. As of January 2025, the total GDPR fines have reached approximately €5.88 billion. (Source: IAPP and Data Privacy Manager)
Share this guide to help others stay secure and private while screen recording.
With the basics of screen recording security in mind, let’s now explore the potential threats and vulnerabilities through detailed attack analysis and threat modeling.
Social Engineering + Screen Recording Phishing
Hackers use phishing emails to induce users to click on malicious links or software. Once the user grants recording permissions, the hackers can capture sensitive operational screens.
Malicious Remote Desktop + Screen Recording
After hackers infiltrate remote desktop control, they initiate screen recording to collect all the victim's operations.
Clipboard + Screen Recording Combined Attack
After a user copies sensitive information, the clipboard content may be captured by software and recorded along with the screen.
Using the six elements of the STRIDE model, we can establish a systematic threat modeling matrix:
Combining the above attack methods, we can construct a "Threat Modeling Matrix":
The horizontal axis represents the attack methods (such as phishing, remote desktop, and clipboard leakage), and the vertical axis represents the risk levels (user end, platform end, and transmission link), to intuitively express the specific risk locations and types of each attack method.
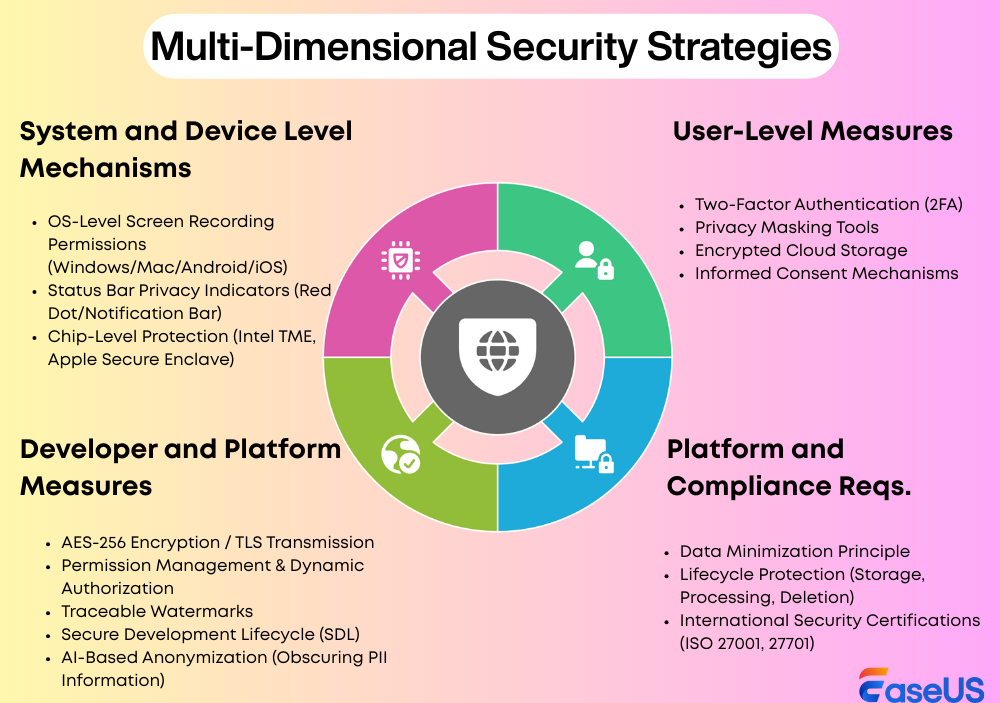
To address the risks associated with screen recording as outlined above, it is essential to design protective mechanisms from multiple dimensions, including users, software developers/platforms, compliance recording standards, and systems and devices.
Share this guide to help others stay secure and private while screen recording.
To delve deeper into the multifaceted issue of screen recording privacy and security, let's examine specific cases across different sectors. Our analysis will highlight key challenges and emerging trends, starting with the education industry.
Compliance Management of Screen Recording on Online Course Platforms
With the explosive growth of global online education, the illegal dissemination of pirated courses and recorded videos has become a major headache for the industry. According to data from The Business Research Company, the global online learning market size is expected to grow to $354.71 billion by 2025 (a year-on-year increase of 13.0%). Screen recording technology plays an important role in course archiving and learning review.
In 2021, an international online education platform experienced a major course leakage: students recorded videos with third-party tools and uploaded them to pirate websites, causing a loss of over 15% of subscriptions.
To address this, the platform implemented compliance measures:
One year later, pirated course leakage dropped by 60%, user complaints decreased, and teacher satisfaction improved. The platform also earned ISO/IEC 27001 certification, enhancing its reputation and brand competitiveness.
AI-Driven Screen Recording Desensitization Practice (Simplified Version)
In B2B scenarios, screen recording is often used for product demonstrations and remote training but may involve customer privacy and sensitive data. A European software company once inadvertently displayed customer email addresses and account information during a recorded demonstration, leading to complaints.
To prevent such leaks, the company introduced AI desensitization technology in 2022:
After implementation, the rate of sensitive information leakage decreased by 80%, and customer satisfaction with data security increased by 22%. This practice was awarded the Best Privacy Technology Application Case of the Year by IAPP.
However, the screen recording industry as a whole still faces multiple challenges:
Lack of Unified Privacy Standards
Different countries and regions have significantly different requirements for screen recording compliance. For example, the GDPR emphasizes “notice and consent,” the PIPL requires “separate consent,” while the CCPA focuses on the “right to access and delete.” When operating across borders, companies need to invest substantial resources to meet multiple standards, increasing compliance costs.
AI Recording Brings New Types of Data Misuse Risks
Emerging AI screen recording tools are equipped with automatic transcription, intelligent tagging, and behavior analysis functions. However, they can also be misused to monitor employee activities and track user habits, triggering privacy and ethical controversies. For instance, some companies have used AI tools for work monitoring without informing their employees, leading to legal disputes in Europe and America.
User's Right to Privacy Notice is Overlooked
Many video conference users are still unaware that they are being recorded. This indicates that a large number of software applications lack clear recording notification mechanisms, and users’ right to be informed about their privacy is not fully protected.
With the widespread adoption of screen recording technology in both corporate and personal settings, privacy and data compliance have become critical concerns. Different regions impose varying legal requirements on the collection, storage, processing, and sharing of recorded content. Organizations must understand and comply with these regulations to avoid legal penalties and reputational damage.
The GDPR is one of the world's strictest privacy protection regulations, and it has clear requirements for screen recording data. In 2021, a European online education platform was fined 500,000 euros by the regulatory authority for recording class videos without obtaining student authorization and was required to make immediate rectifications.
The CCPA in California classifies screen recording content as personal information, and users are granted extensive rights. In practice, companies typically establish user privacy portals to allow users to conveniently exercise their rights to access and delete information.
| Region | Regulation | Screen Recording Requirements | Compliance Focus |
|---|---|---|---|
| European Union | GDPR (General Data Protection Regulation) | Explicit informed consent, data minimization; users must agree to recording, and organizations can only collect necessary information. | Transparency in user consent, cross-border data transfer compliance, data minimization. |
| California, USA | CCPA (California Consumer Privacy Act) | Recorded content is considered personal information; users can request access and deletion of their recorded data. | User rights to access and delete data, privacy disclosure, third-party sharing management. |
| China | PIPL (Personal Information Protection Law) | Explicit notification and separate consent; processing must follow the principle of minimal necessity. | Data processing transparency, obtaining individual consent, lawful storage and transfer. |
To ensure that screen recording operations comply with both international and local privacy regulations, organizations can adopt the following best practices:
Establish a Privacy Impact Assessment (PIA) System
Data Sovereignty and Cross-Border Flow Control
Obtain Compliance Certifications to Enhance Credibility
Practical Implementation Recommendations
Share this guide to help others stay secure and private while screen recording.
As screen recording becomes integral to business—spanning remote collaboration, training, and compliance - the risks of breaches and privacy violations carry direct economic and trust consequences. Security is no longer a technical detail but a business priority.
The IBM 2025 Cost of a Data Breach Report shows the cost fell for the first time in five years, to $4.44 million, primarily due to AI-powered defenses that accelerated breach detection and containment. However, attackers are also leveraging AI to enhance their tactics. Statistics show that 16% of breaches involved AI, primarily in phishing and deepfake attacks.
Furthermore, the 2025 report indicates that the average cost of a breach in the United States is even higher, reaching $10.22 million. 20% of organizations experienced breaches due to "shadow AI," resulting in an average additional $670,000 in losses. Data breaches caused by malicious insiders are particularly costly, averaging $4.99 million.
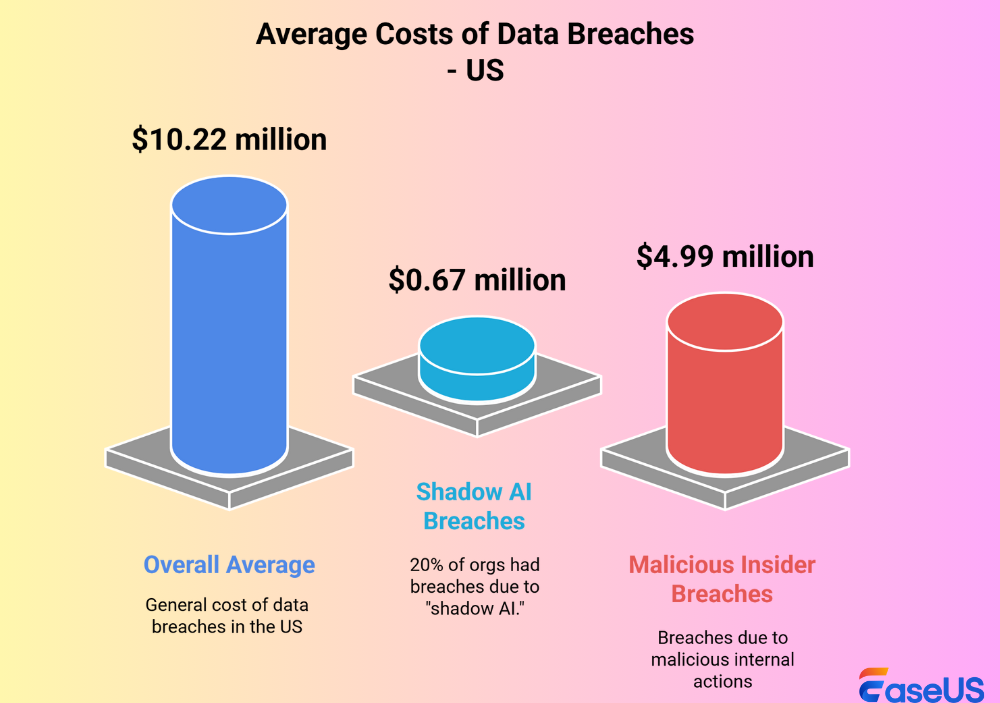
These costs extend far beyond immediate technical remediation. They encompass regulatory fines, forensic investigations, legal proceedings, breach notifications, customer compensation, reputational recovery, and operational downtime. For businesses operating in competitive global markets, such financial shocks can erode shareholder confidence, weaken brand equity, and even jeopardize long-term sustainability.
While security lapses pose economic threats, proactive privacy protection can become a powerful differentiator. In the B2B marketplace, compliance readiness and robust privacy management have emerged as decisive procurement criteria. Enterprises increasingly favor vendors whose solutions come with transparent privacy policies, GDPR/CCPA/PIPL alignment, and certifications such as ISO/IEC 27001 and ISO/IEC 27701. These elements are no longer mere regulatory checkboxes—they are trust signals that directly influence business decisions.
Adopting secure and privacy-conscious screen recording tools not only reduces the probability of costly incidents but also reinforces brand credibility. For instance, EaseUS RecExperts offers enterprises a compliant and reliable solution by integrating features such as encrypted recording, granular access control, and transparent consent mechanisms. Such tools enable businesses to conduct training, knowledge sharing, and compliance recording without exposing themselves to unnecessary risks.
As enterprises accelerate digital transformation, screen recording is shifting from a productivity tool to a compliance-critical and trust-sensitive technology. The future will be defined by how AI innovation and Zero Trust security models integrate to balance usability, security, and privacy.
Artificial Intelligence will play a central role in shaping next-generation screen recording. Key applications include:
Such features will elevate privacy protection from reactive to proactive, making compliance seamless for enterprises.
Current privacy regulations (GDPR, CCPA, PIPL) remain fragmented, but momentum is building toward international harmonization. A unified framework for screen recording compliance could:
This trend toward standardization will reward early adopters who align with international best practices.
For screen recording vendors, security and privacy are not only technical safeguards but strategic assets.
Several technical paradigms are converging to redefine screen recording:
Together, these will set the stage for next-generation secure recording ecosystems.
To prepare for this shift, stakeholders should take the following actions:
Screen recording serves as a bridge for modern communication and collaboration, but it can also become an entry point for privacy breaches. Only through the joint efforts of users, developers, businesses, and regulatory bodies, and by building a multi-dimensional defense from technology, systems, and cultural awareness, can we achieve a secure, trustworthy, compliant, transparent, and user-friendly screen recording ecosystem.
Let us join hands to establish such a trustworthy "digital window" that not only facilitates the efficient transmission of information but also protects the privacy rights of every user.
Share this guide to help others stay secure and private while screen recording.
Was This Page Helpful?
More from EaseUS
Gen Z Media Consumption Report 2026: Trends, Insights & Brand Strategies
![]() Jane Zhou/2026-01-21
Jane Zhou/2026-01-21
2026 Short-Form Video Marketing Trends: Strategies, User Behavior & Brand Insights
![]() Jean/2026-01-21
Jean/2026-01-21
2026 eLearning Video Consumption Statistics and Trends: Data-Backed Insights into Online Learning
![]() Jane Zhou/2026-01-21
Jane Zhou/2026-01-21
Digital Content Strategy in 2026: Key Insights and Strategic Shifts
![]() Jane Zhou/2026-01-21
Jane Zhou/2026-01-21
users.
Success, thanks for submitting!